ASR Custom Data Collection with Intune
At MMS MOA 2023, I presented a session alongside Kenny Buntinx on Attack Surface Reduction (ASR) rules, a session filled with lessons learnt, interaction and Belgian chocolate. During this session, I showed a custom data collection script that I had written to collect the ASR events from the event log and send them to a Log Analytics workspace, and then how to inject that data into a Power BI report.
This post will cover the configuration of the Power BI Report and the Intune Remediation Script, to help you better report on ASR events in your environment, without having to pay for an E5 license.
Getting Prepared
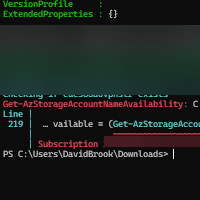
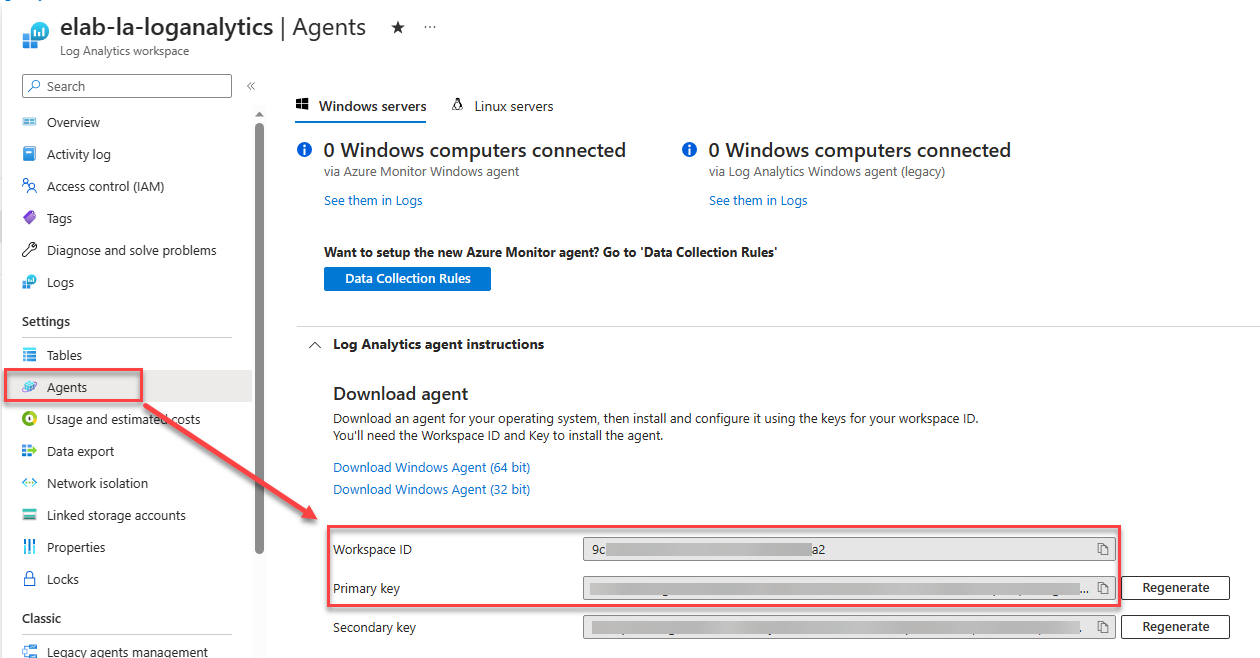
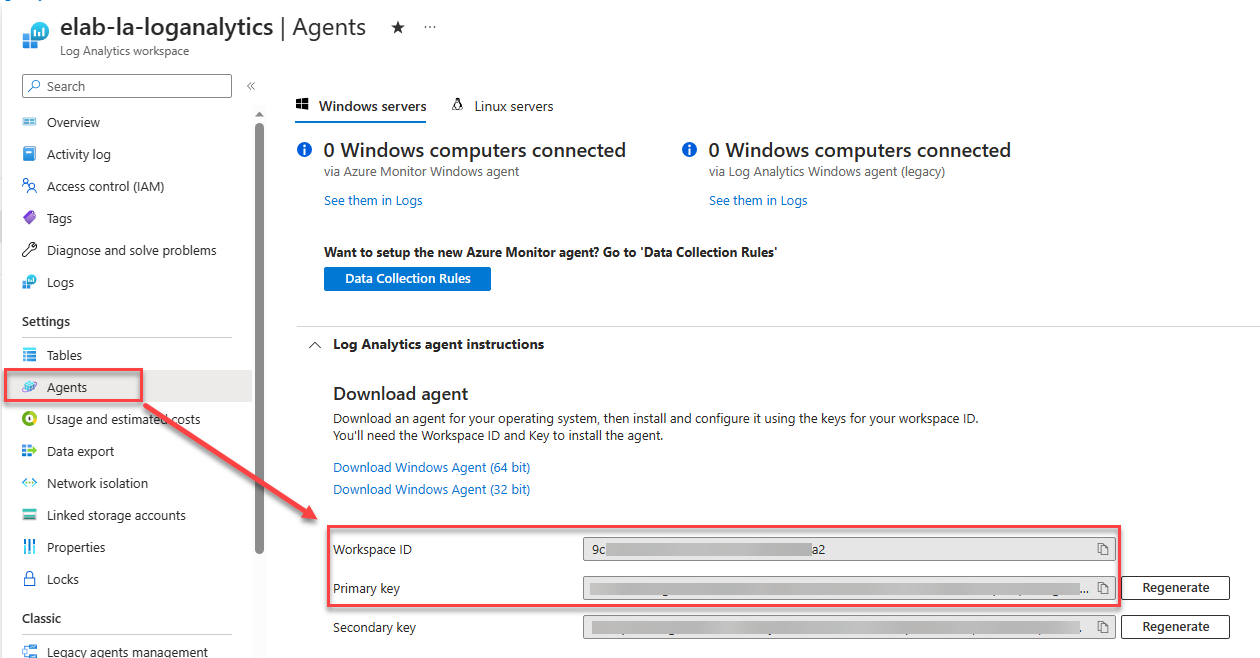
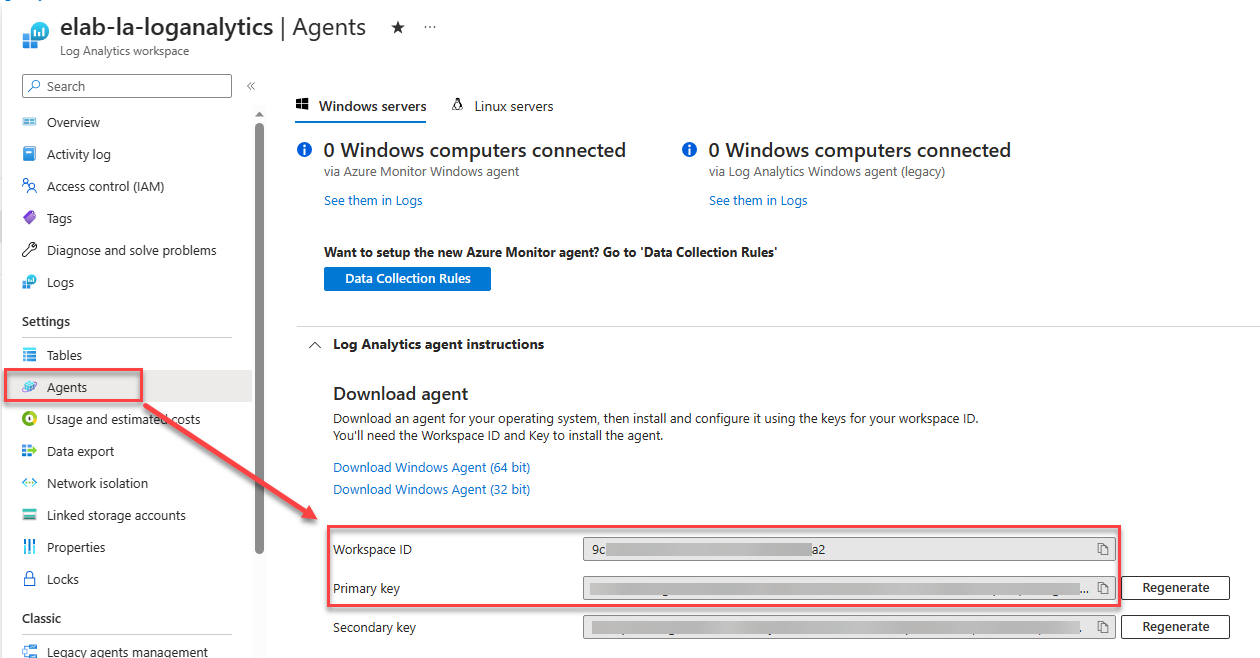
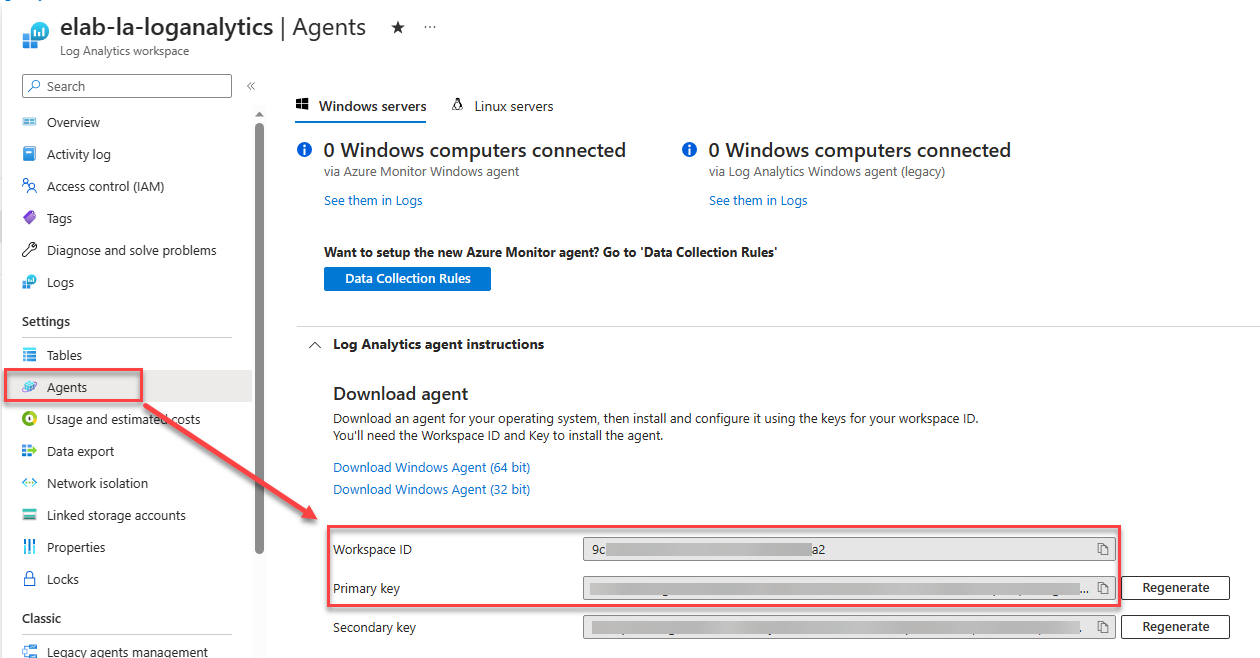
First of all, you will need a Log Analytics Workspace, if you don’t have one already, you can create one in the Azure Portal. Once you have the workspace created, we will need the Workspace ID and Primary Key for the workspace, these can be found in the Agents section of the workspace.
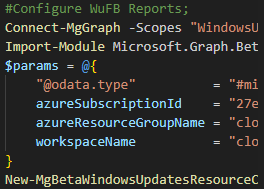
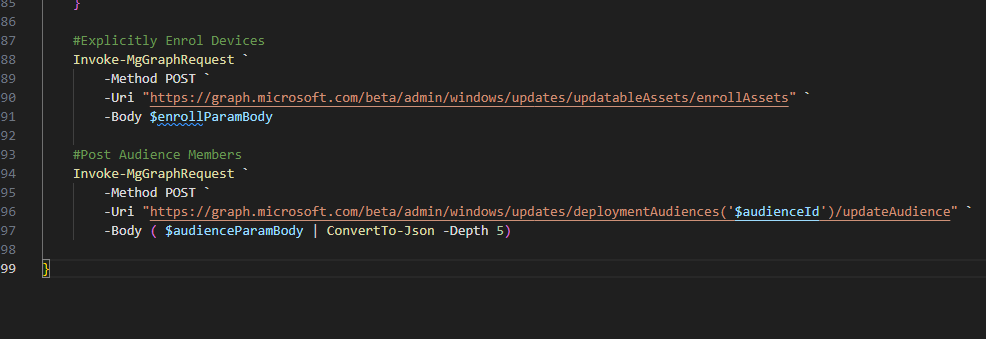
The second thing we will need is the Intune Remediation Script, this is available for download from the below button. The script will need to be configured with the Workspace ID and Primary Key from the Log Analytics Workspace at a minimum, there are other configurable options in the script, but these are optional, and are noted in the HelpMessage of the parameters.
Once the script has been amended, the information on how to configure the tested configuration within Intune is available in the README file in the repository.
Configuring the Power BI Report
Ok, so this section is to assume that there is now data flowing into the Log Analytics Workspace, as without the data, the report will be empty.
The first thing we need to do in this section is create an Azure App Registration that can be used to access both the Log Analytics Workspace and the Graph API.
To do this, we will need to create a new App Registration in the Azure Portal, and give it the following Graph API Application permissions:
- DeviceManagementManagedDevices.Read.All
You can follow my guide on how to create an App Registration here, and then how to grant access to the Log Analytics Workspace here.
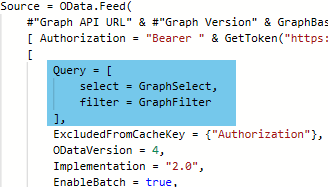
Once the App Registration has been created, we will need to download the Power BI Report, from the below button, and open it in Power BI Desktop.
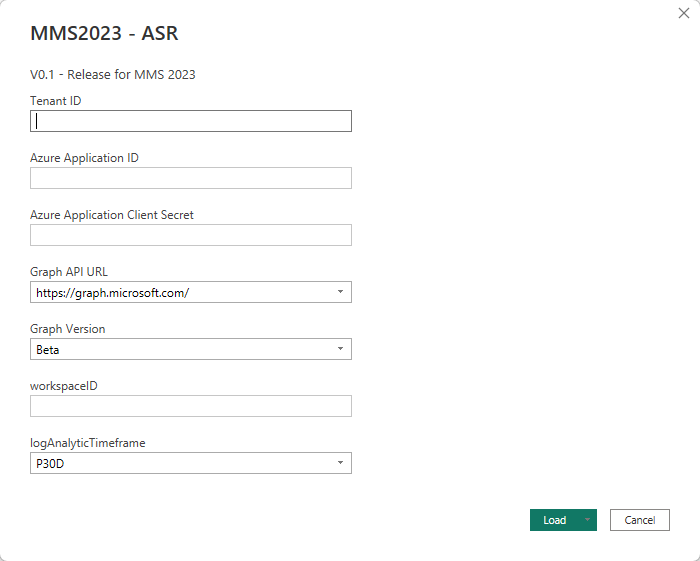
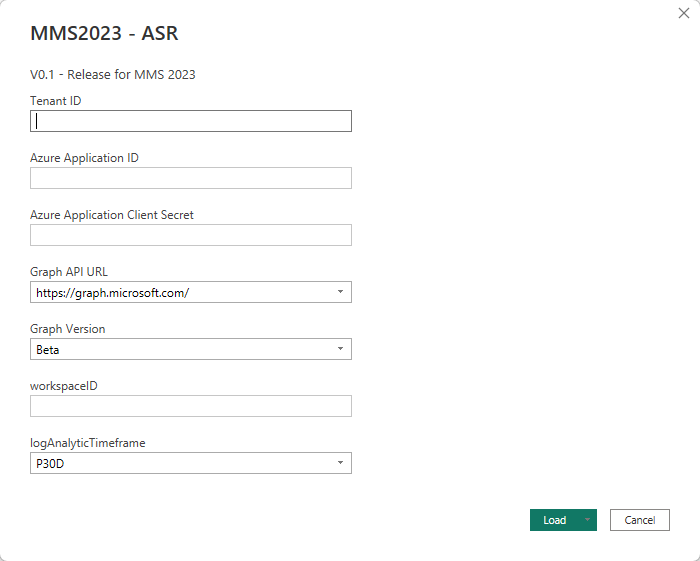
When you first open the report, you will be prompted to enter the following information:
- Tenant ID – This is the tenant ID of the Azure AD Tenant
- Application ID – This is the Application ID of the App Registration
- Application Secret – An application secret key of the App Registration
- Log Analytics Workspace ID – This is the Workspace ID of the Log Analytics Workspace
You will also need to select the Timeframe you wish to query from a drop down list, however this is further configurable in the report itself.
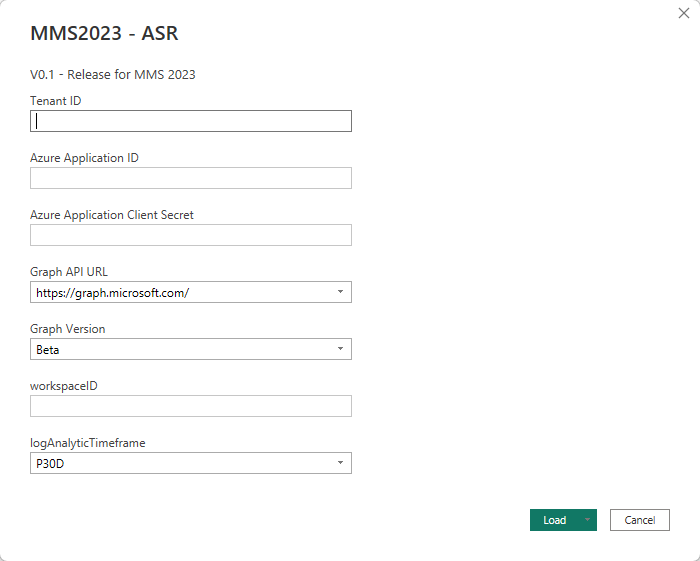
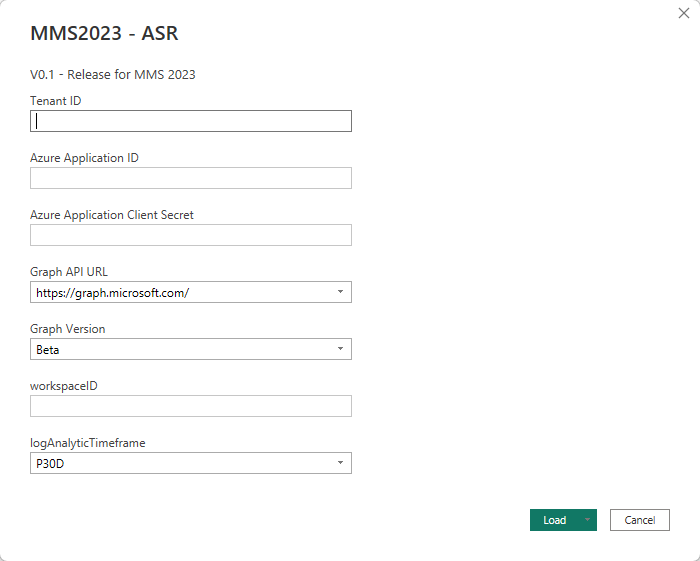
Once you click Load, you will be prompted about privacy levels, ensure you configure these as Public for the purposes of this guide, this is the only configuration that has been tested and confirmed working. This will then initiate the data load from the API’s and Log Analytics Workspace.
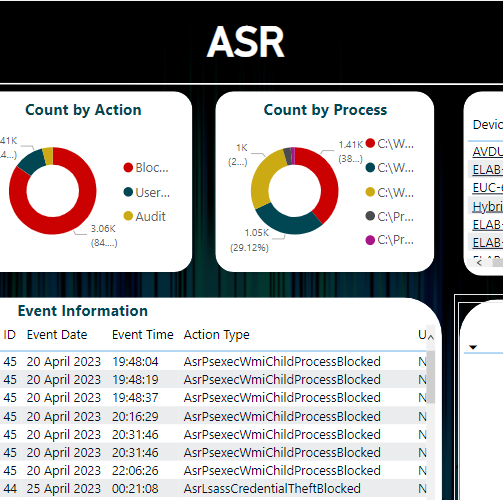
Once the Data has been loaded, you will be presented with the following report visual:
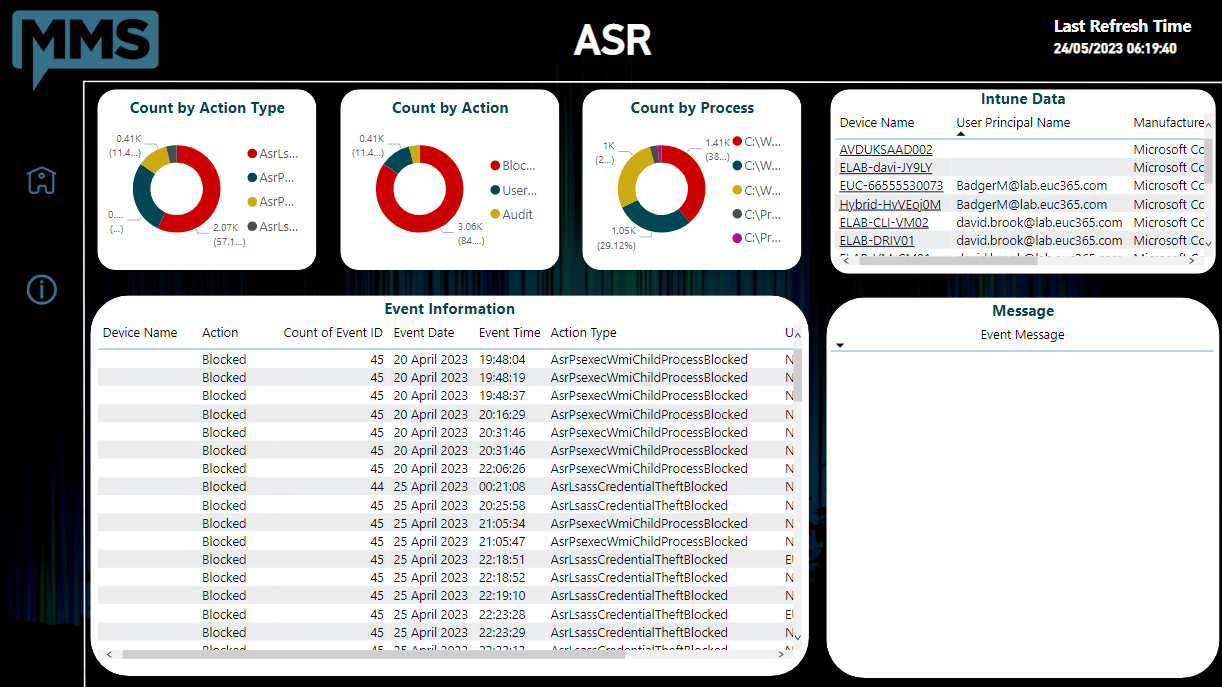
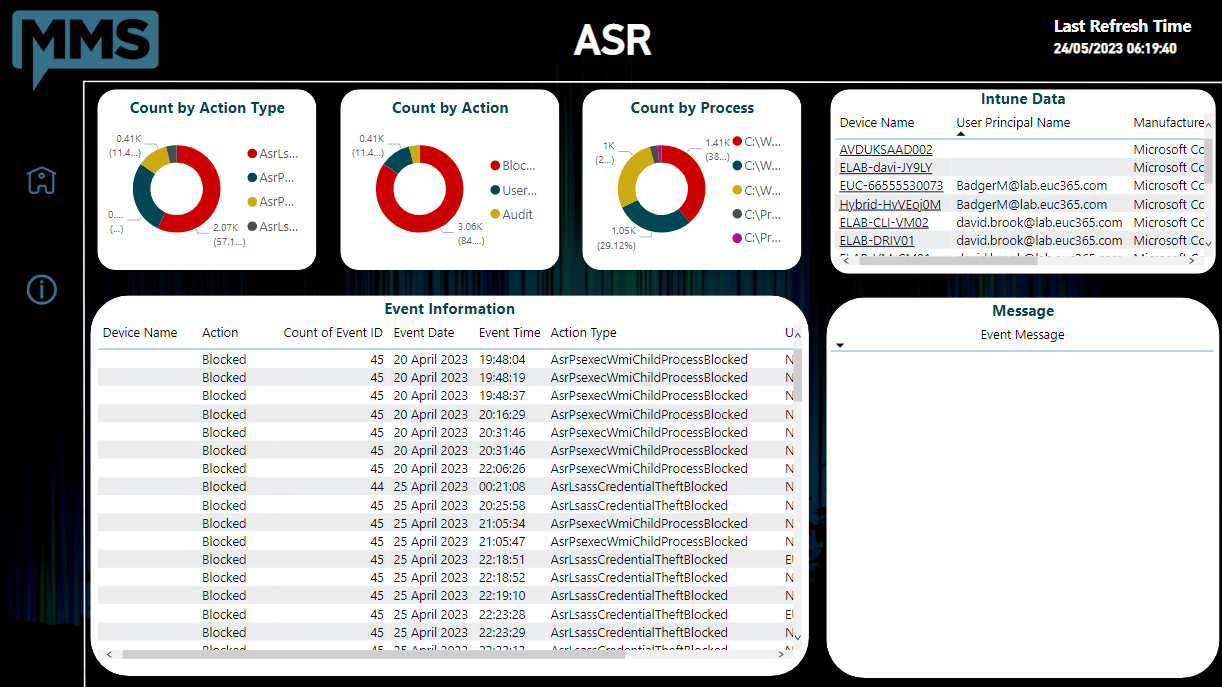
Once you click on an Event in the bottom left-hand table, the event data will be displayed to the right-hand side to help you make informed decisions on your data.
Your Content Goes Here
This post utilises frameworks of the Guys and Girls over at MSEndpointMGR, the function used to post the data to the LAW is based on a function used in other inventory collection scripts.
You can also look to further secure you data collection by utilising one of their other frameworks which utilises Azure Function Apps (SEE HERE)
I hope you find this post useful, and if you have any questions, please reach out to me or leave a comment below.
Categories
Tags
ASR Custom Data Collection with Intune
At MMS MOA 2023, I presented a session alongside Kenny Buntinx on Attack Surface Reduction (ASR) rules, a session filled with lessons learnt, interaction and Belgian chocolate. During this session, I showed a custom data collection script that I had written to collect the ASR events from the event log and send them to a Log Analytics workspace, and then how to inject that data into a Power BI report.
This post will cover the configuration of the Power BI Report and the Intune Remediation Script, to help you better report on ASR events in your environment, without having to pay for an E5 license.
Getting Prepared
First of all, you will need a Log Analytics Workspace, if you don’t have one already, you can create one in the Azure Portal. Once you have the workspace created, we will need the Workspace ID and Primary Key for the workspace, these can be found in the Agents section of the workspace.
The second thing we will need is the Intune Remediation Script, this is available for download from the below button. The script will need to be configured with the Workspace ID and Primary Key from the Log Analytics Workspace at a minimum, there are other configurable options in the script, but these are optional, and are noted in the HelpMessage of the parameters.
Once the script has been amended, the information on how to configure the tested configuration within Intune is available in the README file in the repository.
Configuring the Power BI Report
Ok, so this section is to assume that there is now data flowing into the Log Analytics Workspace, as without the data, the report will be empty.
The first thing we need to do in this section is create an Azure App Registration that can be used to access both the Log Analytics Workspace and the Graph API.
To do this, we will need to create a new App Registration in the Azure Portal, and give it the following Graph API Application permissions:
- DeviceManagementManagedDevices.Read.All
You can follow my guide on how to create an App Registration here, and then how to grant access to the Log Analytics Workspace here.
Once the App Registration has been created, we will need to download the Power BI Report, from the below button, and open it in Power BI Desktop.
When you first open the report, you will be prompted to enter the following information:
- Tenant ID – This is the tenant ID of the Azure AD Tenant
- Application ID – This is the Application ID of the App Registration
- Application Secret – An application secret key of the App Registration
- Log Analytics Workspace ID – This is the Workspace ID of the Log Analytics Workspace
You will also need to select the Timeframe you wish to query from a drop down list, however this is further configurable in the report itself.
Once you click Load, you will be prompted about privacy levels, ensure you configure these as Public for the purposes of this guide, this is the only configuration that has been tested and confirmed working. This will then initiate the data load from the API’s and Log Analytics Workspace.
Once the Data has been loaded, you will be presented with the following report visual:
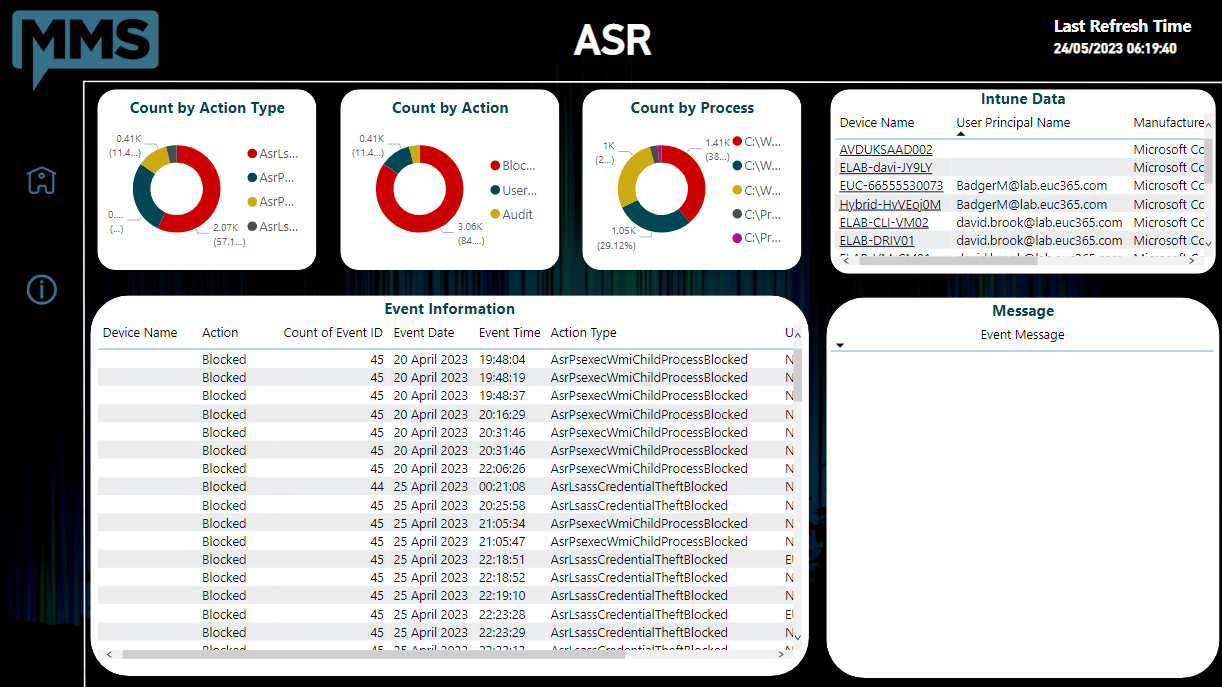
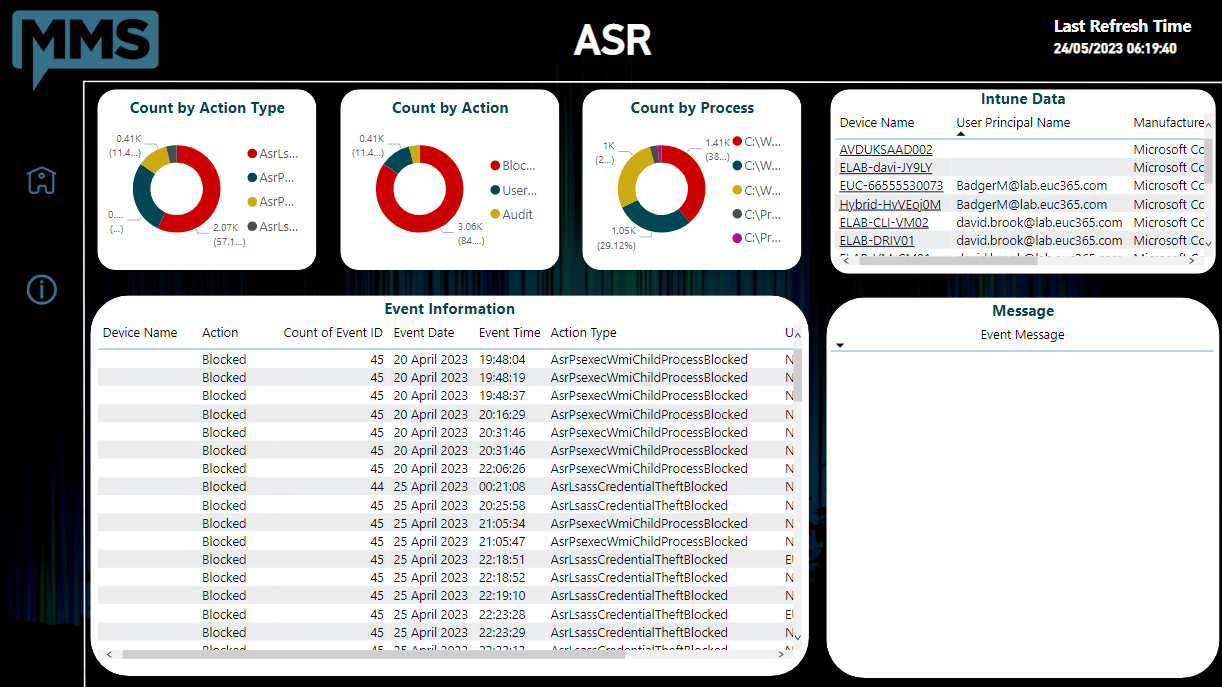
Once you click on an Event in the bottom left-hand table, the event data will be displayed to the right-hand side to help you make informed decisions on your data.
Your Content Goes Here
This post utilises frameworks of the Guys and Girls over at MSEndpointMGR, the function used to post the data to the LAW is based on a function used in other inventory collection scripts.
You can also look to further secure you data collection by utilising one of their other frameworks which utilises Azure Function Apps (SEE HERE)
I hope you find this post useful, and if you have any questions, please reach out to me or leave a comment below.